STIR/SHAKEN Technology: How It Will Impact Your Call Center
All the talk about STIR/SHAKEN (“Secure Telephony Identity Revisited”/“Secure Handling of Asserted information using toKENs”) has many companies wondering how it may impact their operations. Rest assured, TCN is taking active measures to prepare for STIR/SHAKEN’s implementation and minimize the burden on our clients. Importantly, our clients will not need to do anything to take advantage of STIR/SHAKEN’s attestation framework and better ensure that their calls are authenticated.
What is STIR/SHAKEN?
STIR/SHAKEN is an industry-developed framework used to authenticate callers in real-time, which allows voice service providers and consumers to more easily identify illegal calls. By making it more difficult for illegal callers to reach consumers, STIR/SHAKEN can reduce the number (and harmful impact of) illegal calls.
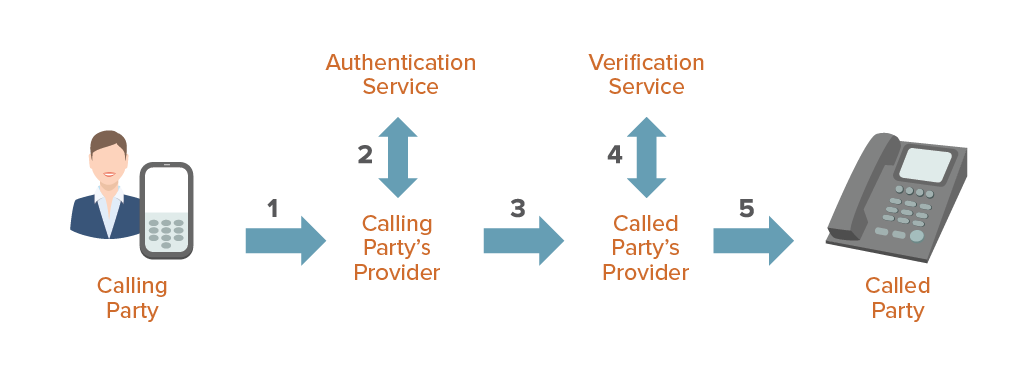
Under STIR/SHAKEN, a basic call flow looks like this:
To authenticate a call, STIR/SHAKEN relies on verifiable digital certificates provided by a trusted authentication service. The certificates allow service providers to attest to the legitimacy of a calling party’s number. The degree of authentication can vary depending on the circumstances of each call, creating different levels of trustworthiness. There are three different levels of attestation, and each level indicates a different degree of trustworthiness regarding the call’s source:
- Full Attestation. The service provider has authenticated the calling party, and the calling party is authorized to use the calling number. For example, a call made by a subscriber registered with the originating telephone service provider’s soft switch would receive full attestation.
- Partial Attestation. The service provider has authenticated the call’s origination (e.g., a known customer) but cannot verify whether the call’s source is authorized to use the calling number. For example, a call from a telephone number behind an enterprise’s private branch exchange (“PBX”) that uses an unknown extension would receive partial attestation.
- Gateway Attestation. The service provider has authenticated the source from which it received the call but cannot authenticate the call source. For example, a call received from an international gateway, with no further authenticated information, would receive gateway attestation.
TCN is taking measures to successfully integrate STIR/SHAKEN into our services.
Clients will not need to do anything to take advantage of STIR/SHAKEN’s attestation framework when it is implemented and better ensure that their calls are authenticated.
We plan to offer Full Attestation and Partial Attestation for all numbers that clients acquire through us as soon as attestation levels are available from our voice service providers. (Industry groups are still developing criteria for receiving Full Attestation and Partial Attestation, so we cannot yet say what level of attestation we will provide when.)
Please keep in mind: Clients that do not port their numbers to TCN (i.e., port source and caller ID information) will receive Gateway Attestation. To gain a higher attestation level, clients may port their numbers to TCN.
Why is the industry implementing STIR/SHAKEN?
To increase consumer confidence in the telephone network, industry standards groups began developing STIR/SHAKEN to help combat scammers, fraudsters, and other illegal callers. Additionally, some voice service providers have lobbied lawmakers to require STIR/SHAKEN as part of a legal framework that would allow those voice service providers to block calls that fail STIR/SHAKEN.
By law, Canadian voice service providers must implement STIR/SHAKEN by September 30, 2020. U.S. voice service providers must implement STIR/SHAKEN by June 30, 2021.
In the United States, the TRACED Act – which became law on December 30, 2019 – requires the FCC to develop new regulations that create:
- A safe harbor for voice service providers that implement and follow STIR/SHAKEN’s framework but unintentionally or inadvertently misidentify a call’s authentication level; and
- Recourse for callers whose calls are misidentified, which will allow callers to have their calls correctly authenticated.
Importantly, the TRACED Act tasks the FCC with implementing the safe harbor and recourse process. Furthermore, voice service providers’ industry groups (e.g., CTIA, NCTA, and USTelecom) have already begun lobbying the FCC for a broad safe harbor that would allow voice service providers to block a greater number of calls, including legal calls.
We’ve participated in FCC proceedings to get the best results for callers like our clients – that is, legitimate, compliance-minded businesses in the outbound calling and contact center space – and we continue to closely monitor developments at the FCC. We believe staying at the forefront of regulation, business, and technical compliance pays dividends for our clients, especially as the technical, regulatory, and commercial environments change.
If you have further questions about STIR/SHAKEN and TCN’s ability to help you reach your customers, please feel free to download our whitepaper here or check out this webinar for more information.