TCN to End Support for TLS 1.0
TLS 1.0 Support Ends May 31, 2017
TCN will discontinue TLS 1.0 support on May 31, 2017. On that date during a maintenance window at the end of day TCN will disable TLS 1.0 on all services. Action is required prior to this date to prevent any disruption to access of TCN services. This article contains information to help our clients navigate this important security change. After May 31, 2017 TLS 1.1 or TLS 1.2 will be required to use TCN’s services.
What is TLS?
TLS stands for “Transport Layer Security”. It is a protocol that provides privacy and data integrity between two communication applications. It’s the most widely deployed security protocol used today, and is used for web browsers and other applications that require data to be securely exchanged over a network. TLS ensures that a connection to a remote endpoint is the intended endpoint through encryption and endpoint identity verification. The versions of TLS, to date, are 1.0, 1.1, and 1.2. TCN’s web and API services use TLS as a key component of their security.
Why Is This Change Required?
TCN’s highest priority is the safety of our customers data and communications. In an effort to maintain the highest security standards and compliance with PCI DSS 3.2, TCN will require TLS 1.1 or higher after May 31, 2017.
How Will Customers Be Impacted?
After TCN disables TLS 1.0 any connection attempts using TLS 1.0 will fail. This will impact all of TCN’s web and API services.
How Can Customers Avoid A Service Disruption?
The action required by your organization will depend on what applications, tools, and versions of said methods you use to access TCN’s services.
Internet Browsers
Your organization will experience issues accessing TCN services if you have disabled the supported encryption protocols or if you are using an unsupported browser.
Supported Browsers
- Mozilla Firefox, recent stable versions 27.0 or higher
- Microsoft Internet Explorer versions 9, 10, 11
- Google Chrome (no Java), recent stable versions 38 or higher
- Apple Safari versions 7.x, 8.x, 9.x, 10.x
If you are able to view our TLS TEST SITE, which has TLS 1.0 disabled, without errors, then access to TCN’s web services via your browser should not be impacted by this change, and no action is required.
If You Experience Errors
You need to ensure your browser is compatible with TLS 1.1 or higher. The minimum required action is to enable TLS 1.1 and/or TLS 1.2 encryption protocol within your browsers security settings. Although we recommend disabling TLS 1.0 for a more secure browsing environment, it is not required. For example, if a user has protocols TLS 1.0, TLS 1.1, and TLS 1.2 enabled within their browsers security settings, they will be able to successfully connect to TCN services with that browser after TCN disables TLS 1.0 support on May 31, 2017.
Older supported versions of Microsoft Internet Explorer (less than version 11) do not enable TLS 1.1 or TLS 1.2 by default. The minimum required action is to enable TLS 1.1 and/or TLS 1.2 encryption protocol within your browsers security settings.
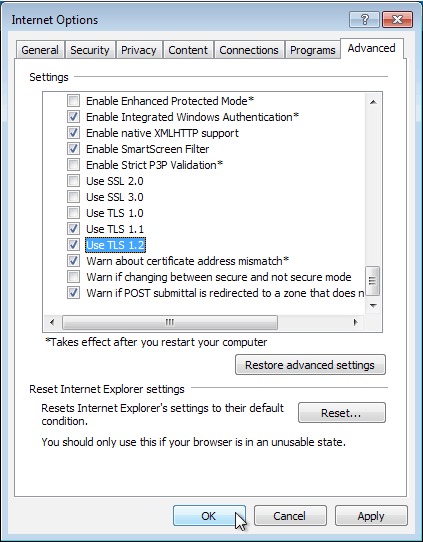
- Click “Tools”, and then select “Internet Options”.
- Click the “Advanced” tab, and then select “Use TLS 1.1” and “Use TLS 1.2”.
- Click “OK” to save.
Here’s an example:
API Integration
API integrations are interfaces or applications that interact with TCN services programmatically. If you have any API integrations, please ensure that the TLS 1.1 and/or TLS 1.2 encryption protocols are supported and/or enabled. If your integrations do not have TLS 1.1 and/or TLS 1.2 enabled after May 31, 2017, your integrations may experience disruption. We recommend that you begin planning to support TLS 1.1 and TLS 1.2 as soon as possible.
Common Platforms and Compatibility Notes:
- Java 8; Compatible with TLS 1.1 or higher by default.
- Java 7; NOT compatible by default. Enable TLS 1.1 and TLS 1.2 using the https.protocols Java system property for HttpsURLConnection.
- Java 6; NOT compatible.
- .NET 4.6 or higher; Compatible with TLS 1.1 or higher by default.
- .NET 4.5 to 4.5.2; NOT compatible by default. .NET applications may directly enable TLS 1.1 and TLS 1.2 in their software code by setting System.Net.ServicePointManager.SecurityProtocol to enable SecurityProtocolType.Tls12 and SecurityProtocolType.Tls11.
- .NET less than 4.5; NOT compatible.
- Python 2.7.9 or higher; Compatible with TLS 1.1 or higher by default.
- Python 2.7.8 or below; NOT compatible.
- Ruby 2.0.0; TLS 1.2 is enabled by default when used with OpenSSL 1.0.1 or higher. Using the :TLSv1_2 (preferred) or :TLSv1_1 symbols with an SSLContext’s ssl_version helps ensure that TLS 1.0 or earlier is disabled.
- Ruby 1.9.3; The :TLSv1_2 symbol does not exist in 1.9.3 and below, but it is possible to patch Ruby to add that symbol and compile Ruby with OpenSSL 1.0.1 or higher.
- OpenSSL 1.0.1 or higher; Compatible with TLS 1.1 or higher by default.
- OpenSSL 1.0.0 or below; Not compatible with TLS 1.1 or higher encryption.